Official 2014 Latest Microsoft 70-412 Exam Dump Free Download(211-220)!
QUESTION 211
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Node1 and Node2. Node1 and Node2 run Windows Server 2012 R2. Node1 and Node2 are configured as a two-node failover cluster named Cluster2. The computer accounts for all of the servers reside in an organizational unit (OU) named Servers. A user named User1 is a member of the local Administrators group on Node1 and Node2. User1 creates a new clustered File Server role named File1 by using the File Server for general use option. A report is generated during the creation of File1 as shown in the exhibit. (Click the Exhibit button.)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00118_thumb.jpg)
File1 fails to start.
You need to ensure that you can start File1. What should you do?
A. Log on to the domain by using the built-in Administrator for the domain, and then recreate the clustered
File Server role by using the File Server for general use option.
B. Recreate the clustered File Server role by using the File Server for scale-out Application data option.
C. Assign the computer account permissions of Cluster2 to the Servers OU.
D. Assign the user account permissions of User1 to the Servers OU.
E. Increase the value of the ms-DS-MachineAccountQuota attribute of the domain.
Answer: B
QUESTION 212
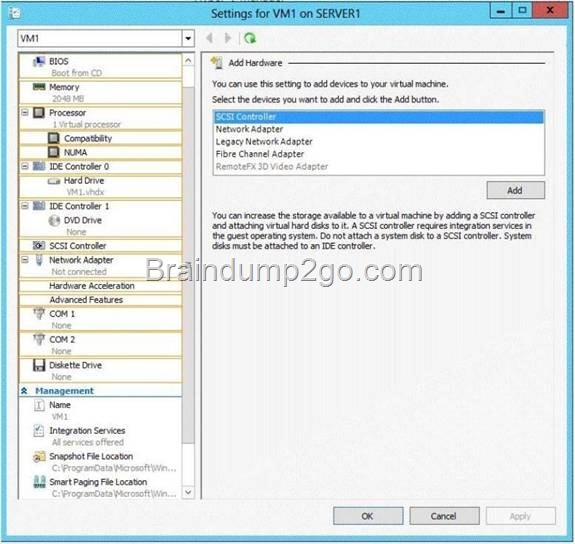
Your network contains two servers named Server1 and Server 2. Both servers run Windows Server 2012 R2 and have the Hyper-V server role installed. Server1 hosts a virtual machine named VM1. The virtual machine configuration files and the virtual hard disks for VM1 are stored in D: \VM1.
You shut down VM1 on Server1.
You copy D:\VM1 to D:\VM1 on Server2.
You need to start VM1 on Server2. You want to achieve this goal by using the minimum amount of administrative effort.
What should you do?
A. Run the Import-VMIntialReplication cmdlet.
B. Create a new virtual machine on Server2 and attach the VHD from VM1 to the new virtual machine.
C. From Hyper-V Manager, run the Import Virtual Machine wizard.
D. Run the Import-IscsiVirtualDisk cmdlet.
Answer: C
QUESTION 213
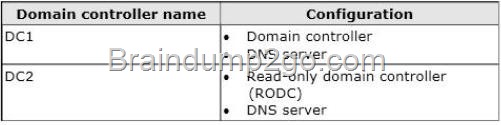
Your network contains an Active Directory forest. The forest contains one domain named adatum.com. The domain contains three domain controllers. The domain controllers are configured as shown in the following table.
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00120_thumb.jpg)
DC2 has all of the domain-wide operations master roles. DC3 has all of the forest-wide operation master roles. You need to ensure that you can use Password Settings objects (PSOs) in the domain.
What should you do first?
A. Uninstall Active Directory from DC1.
B. Change the domain functional level.
C. Transfer the domain-wide operations master roles.
D. Transfer the forest-wide operations master roles.
Answer: A
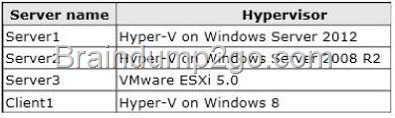
QUESTION 214
Your network contains an Active Directory forest named contoso.com. The forest contains three domains. All domain controllers run Windows Server 2012 R2. The forest has a two-way realm trust to a Kerberos realm named adatum.com. You discover that users in adatum.com can only access resources in the root domain of contoso.com. You need to ensure that the adatum.com users can access the resources in all of the domains in the forest.
What should you do in the forest?
A. Delete the realm trust and create a forest trust.
B. Delete the realm trust and create three external trusts.
C. Modify the incoming realm trust.
D. Modify the outgoing realm trust.
Answer: D
QUESTION 215
Your network contains an Active Directory domain named contoso.com. The domain contains two domain controllers named DC1 and DC2 that run Windows Server 2012 R2. DC1 and DC2 fail to replicate Active Directory information. You confirm that DC1 and DC2 have network connectivity. The NTDS Settings of DC2 are configured as shown in the NTDS Settings exhibit. (Click tie Exhibit button.)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00122_thumb.jpg)
DNS is configured as shown in the DNS exhibit. (Click the Exhibit button.)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0026_thumb.jpg)
You need to ensure that DC1 and DC2 can replicate immediately. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. From DC1, restart the Netlogon service.
B. From DC2, run nltest.exe /sync.
C. From DC1, run ipconfig /flushdns.
D. From DO, run repadmin /syncall.
E. From DC2, run ipconfig /registerdns.
F. From DC2, restart the Netlogon service.
Answer: DE
Explanation:
The DC2 name/alias is not available in DNS.
First we register the DC2 name from DC with the ipcpnfig /registerdns. (E) Then we synchronizes a specified domain controller DC1 (DC2 would also work) with all of its replication partners with repadmin /syncall. (D)
QUESTION 216
Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012 R2. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. Cluster1 contains a Clustered Shared Volume (CSV). A developer creates an Application named App1. App1 is NOT a cluster-aware Application. App1 stores data in the file system. You need to ensure that App1 runs in Cluster1. The solution must minimize development effort.
Which cmdlet should you run?
A. Add-ClusterGenericServiceRole
B. Add-ClusterServerRole
C. Add-ClusterGenericApplicationRole
D. Add-ClusterScaleOutFileServerRole
Answer: C
Explanation:
* Add-ClusterGenericApplicationRole
Configure high availability for an application that was not originally designed to run in a failover cluster.
* If you run an application as a Generic Application, the cluster software will start the application, then periodically query the operating system to see whether the application appears to be running. If so, it is presumed to be online, and will not be restarted or failed over.
QUESTION 217
You have a server named Server1 that runs Windows Server 2012 R2.
You start Server1 by using Windows PE.
You need to repair the Boot Configuration Data (BCD) store on Server1.
Which tool should you use?
A. Bootim
B. Bootsect
C. Bootrec
D. Bootcfg
Answer: C
QUESTION 218
Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2. All servers run Windows Server 2012 R2. Server1 and Server2 have the Failover Clustering feature installed. The servers are configured as nodes in a failover cluster named Cluster1. Cluster1 contains a Clustered Shared Volume (CSV). A developer creates an application named Appl. App1 is NOT a cluster-aware application. App1 stores data in the file system. You need to ensure that App1 runs in Cluster1. The solution must minimize development effort. Which cmdlet should you run?
A. Add-ClusterServerRole
B. Add-ClusterGenericServiceRole
C. Add ClusterScaleOutFileServerRole
D. Add ClusterGenericApplicationRole
Answer: D
Explanation:
* Add-ClusterGenericApplicationRole Configure high availability for an application that was not orig
inally designed to run in a failover cluster.
* If you run an application as a Generic Application, the cluster software will start the application, then periodically query the operating system to see whether the application appears to be running. If so, it is presumed to be online, and will not be restarted or failed over.
QUESTION 219
Hotspot Question
Your network contains three Application servers that run Windows Server 2012 R2. The Application servers have the Network Load Balancing (NLB) feature installed. You create an NLB cluster that contains the three servers. You plan to deploy an Application named App1 to the nodes in the cluster. App1 uses TCP port 8080 and TCP port 8081.
Clients will connect to App1 by using HTTP and HTTPS. When clients connect to App1 by using HTTPS, session state information will be retained locally by the cluster node that responds to the client request.
You need to configure a port rule for App1. Which port rule should you use? To answer, select the appropriate rule in the answer area.
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0028_thumb.jpg)
Answer:
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00210_thumb.jpg)
QUESTION 220
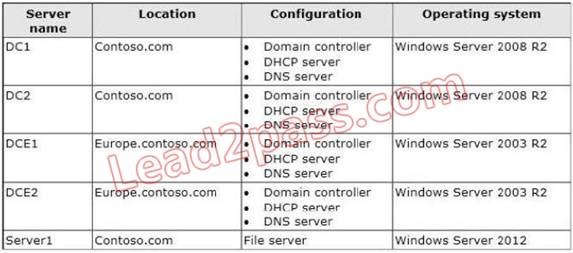
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2. The servers have the Hyper- V server role installed.
A certification authority (CA) is available on the network. A virtual machine named vml.contoso.com is replicated from Server1 to Server2. A virtual machine named vm2.contoso.com is replicated from Server2 to Server1. You need to configure Hyper-V to encrypt the replication of the virtual machines. Which common name should you use for the certificates on each server? To answer, configure the appropriate common name for the certificate on each server in the answer area.
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00124_thumb.jpg)
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00128_thumb.jpg)
Passing Microsoft 70-412 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-412 Dump: http://www.braindump2go.com/70-412.html
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00126_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0018_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image0024_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_9B0A/clip_image00116_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00222_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00114_thumb.jpg)
![clip_image002[24] clip_image002[24]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00224_thumb.jpg)
![clip_image002[26] clip_image002[26]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00226_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00116_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00118_thumb.jpg)
![clip_image002[28] clip_image002[28]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00228_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00120_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image0016_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image0028_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00214_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00216_thumb.jpg)
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00218_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00220_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/c24a1eb24e4f_776C/clip_image00110_thumb.jpg)
![clip_image001[52] clip_image001[52]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00152_thumb.jpg)
![clip_image001[54] clip_image001[54]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00154_thumb.jpg)
![clip_image001[56] clip_image001[56]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00156_thumb.jpg)
![clip_image002[64] clip_image002[64]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00264_thumb.jpg)
![clip_image001[58] clip_image001[58]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00158_thumb.jpg)
![clip_image001[60] clip_image001[60]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00160_thumb.jpg)
![clip_image002[44] clip_image002[44]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00244_thumb.jpg)
![clip_image002[46] clip_image002[46]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00246_thumb.jpg)
![clip_image001[36] clip_image001[36]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00136_thumb.jpg)
![clip_image002[48] clip_image002[48]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00248_thumb.jpg)
![clip_image002[50] clip_image002[50]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00250_thumb.jpg)
![clip_image002[52] clip_image002[52]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00252_thumb.jpg)
![clip_image002[54] clip_image002[54]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00254_thumb.jpg)
![clip_image001[38] clip_image001[38]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00138_thumb.jpg)
![clip_image001[40] clip_image001[40]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00140_thumb.jpg)
![clip_image002[56] clip_image002[56]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00256_thumb.jpg)
![clip_image001[42] clip_image001[42]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00142_thumb.jpg)
![clip_image002[58] clip_image002[58]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00258_thumb.jpg)
![clip_image001[44] clip_image001[44]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00144_thumb.jpg)
![clip_image002[60] clip_image002[60]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00260_thumb.jpg)
![clip_image002[62] clip_image002[62]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00262_thumb.jpg)
![clip_image001[46] clip_image001[46]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00146_thumb.jpg)
![clip_image001[48] clip_image001[48]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00148_thumb.jpg)
![clip_image001[50] clip_image001[50]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A25E/clip_image00150_thumb.jpg)